Kali Linux (BackTrack 6) Released – Download DVD ISO Images
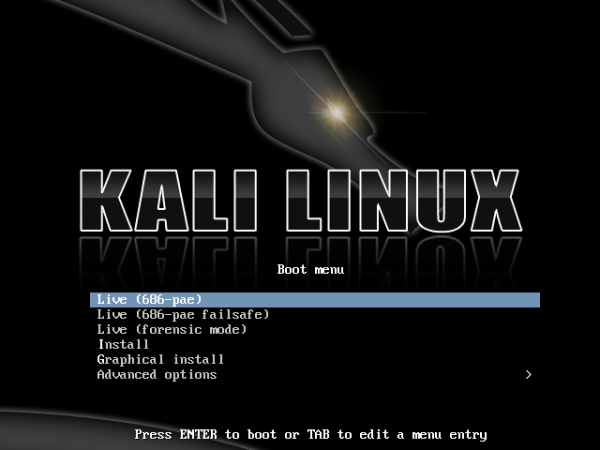
Kali Linux (formerly known as BackTrack Linux) announced the release of Kali Linux Version 1.0.5 recently.Kali Linux is a Debian based distribution specially focused on penetration testing and digital forensics use.From Project PageKali Linux is the new generation of the industry-leading BackTrack Linux penetration testing and security auditing...
Read more


